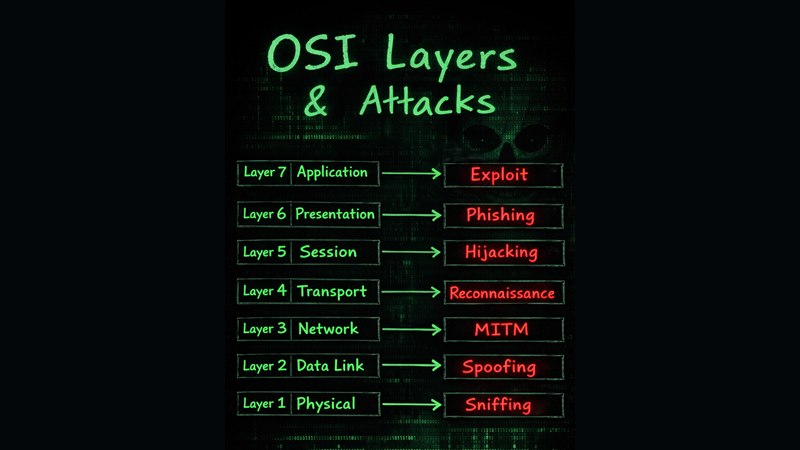
Foundations of Networking Notebook
A beginner-friendly guide to networking fundamentals, breaking down how the internet really works. Covers
TCP vs UDP, IP addressing, DNS, OSI & TCP/IP models, IPv4 vs IPv6, and Wi-Fi security basics. Perfect for
students and tech enthusiasts building strong networking foundations.
View: Networking Notebook (AIUB
Cybersecurity & Programming Society)
Notebook
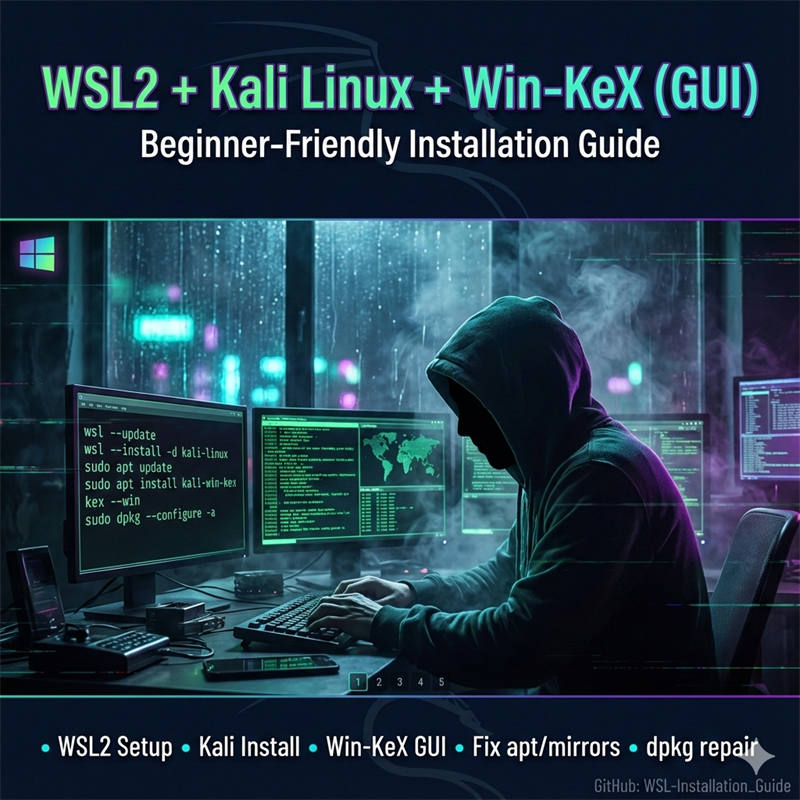
Ultimate Bash Script Handbook
From my first echo "Hello World" to real-world automation, this Bash Scripting Handbook documents my
complete learning journey—covering core concepts, scripting logic, debugging, security, and practical
projects. A hands-on roadmap for mastering Bash and Linux automation. 🐧⚙️
View: Bash Script Handbook (AIUB
Cybersecurity & Programming Society)
Notebook
Python for Cybersecurity – The Practical Hacker’s Handbook!
An intermediate-to-advanced handbook focused on using Python for real-world cybersecurity. Covers
automation, secure coding, powerful libraries, and hands-on ethical hacking projects. Built for learners who
want practical skills, not just theory.
View:
Python for Cybersecurity Handbook (AIUB Cybersecurity & Programming Society)
Notebook
Web Vulnerability Scanner + Ai Support
PoliteWebScanner is a learning-grade web vulnerability scanner plus AI-assisted report viewer. It crawls
safely (queue-based, robots-aware, rate-limited), detects common issues (security headers, cookie flags,
reflected XSS heuristics, SQL error patterns), and exports human-friendly JSON/HTML reports with optional AI
help for triage and remediation
View repo:
Web Vulnerability Scanner
Tooling + CyberSecurity Assistant
A Pythonic Hackathon
Sagar is a Python-based command-line virtual assistant for CSE students and cybersecurity learners. It
supports single-line and multi-line commands to open trusted websites, play curated music links, and answer
questions using an AI model—designed for safe automation, learning, and terminal-first exploration.
View repo: A
Pythonic Hackathon
CyberSecurity Assistant
SharpLink URL 2-Allies
A clean Flask-based URL shortener that converts long links into short, shareable URLs with optional custom
aliases, expiration support, and TinyURL mirroring. Uses SQLite for persistence, includes copy helpers, rate
limiting, and a simple REST API. Ideal for learning backend fundamentals and deployment.
View repo:
SharpLink URL Shortener
Web Dev
Email Scraper
A clean Flask-based URL shortener that converts long links into short, shareable URLs with optional custom
aliases, expiration support, and TinyURL mirroring. Uses SQLite for persistence, includes copy helpers, rate
limiting, and a simple REST API. Ideal for learning backend fundamentals and deployment.
View repo:
Scraper
Web Dev
A_Pythonic-Keylogger
Python-based keylogger for ethical use, capturing keystrokes and emailing logs. Features include retry logic
for email delivery, log file management, and cross-platform support (Windows/Linux). Configurable for
auto-start via systemd or Startup folder. Designed for educational purposes, penetration testing with
consent, and self-monitoring.
View repo: A
Pythonic Keylogger
CyberSecurity
Spech_to_Spech_AI-Assistant
This Python script creates a voice-controlled virtual assistant using speech recognition, AI responses, and
text-to-speech conversion. It listens for commands like opening websites or playing music, processes them
using AI, and responds via speech. Powered by Google’s Speech Recognition, Groq API, and pyttsx3 for voice
interaction.
View repo:
Speech-to-Speech AI Assistant
AI
WebSource Harvester
WebSource Harvester is an educational web-source harvester that crawls a site (BFS, depth-controlled),
downloads browser-visible assets (HTML, CSS, JS, images, fonts, PDFs), and rewrites paths so pages work
offline, including nested routes. It enforces same-origin limits and is designed for learning, offline
analysis, and safe portfolio demos.
View repo:
WebSource Harvester
WebTech
My more works
NoteBooks AND Facebook Community Group


- NOTE: To find more notebooks, projects, tips and tricks like this, join my Facebook
community group and check the featured section for notebooks and explore the Posts to discover real-world
projects.
AIUB CyberSecurity & Programming Society
Useful Repositories




AI Based Projects





Tools/Automation











Networking




Development


















Small Projects





Collected Projects








_page.jpg)
