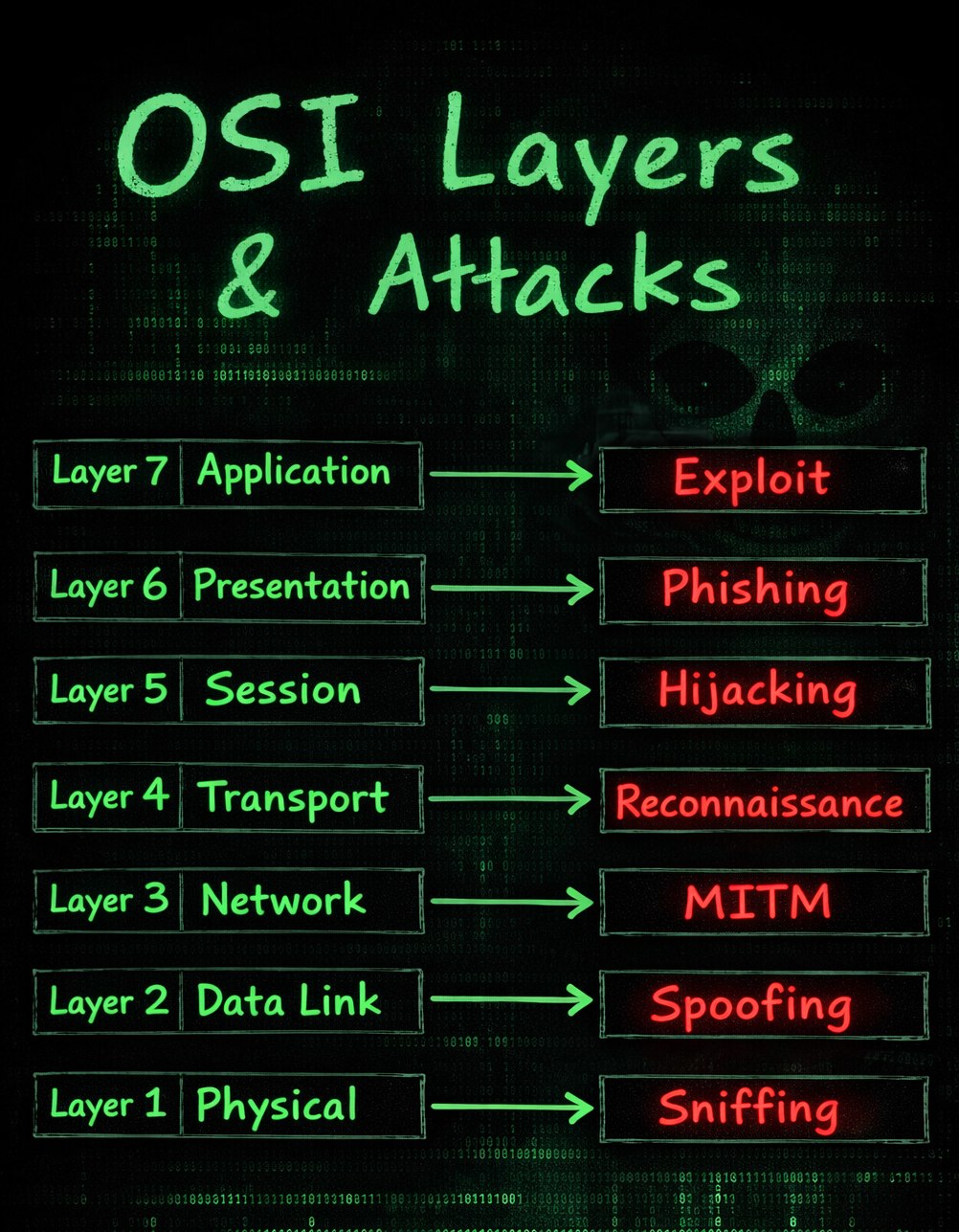
Layer 7 - Application layer
Attack type: Exploit attacks.
- SQL injection to bypass authentication or leak data.
- Cross-site scripting (XSS) to run malicious scripts in a browser.
- Remote code execution through vulnerable and unpatched apps.
Layer 6 - Presentation layer
Attack type: Phishing and trust abuse.
- Fake bank or company emails asking for credentials.
- Malicious PDF attachments that trigger malware execution.
- Certificate spoofing attempts that trick users into trusting a fake site.
Layer 5 - Session layer
Attack type: Session hijacking.
- Stealing session cookies on insecure public Wi-Fi.
- Reusing a valid session ID to access another user account.
- Session fixation where an attacker forces a known session token.
Layer 4 - Transport layer
Attack type: Reconnaissance.
- TCP SYN scans to enumerate open ports.
- UDP scans to detect exposed services.
- Port mapping of services like 22, 80, and 443.
Layer 3 - Network layer
Attack type: Man-in-the-middle (MITM).
- IP spoofing to impersonate trusted hosts.
- Routing manipulation to redirect traffic through attacker systems.
- ICMP redirect abuse to alter packet paths.
Layer 2 - Data link layer
Attack type: Local network spoofing.
- ARP spoofing to intercept traffic in a local segment.
- MAC spoofing to bypass weak access controls.
- VLAN hopping attempts to move across isolated segments.
Layer 1 - Physical layer
Attack type: Physical compromise and sniffing.
- Plugging into exposed ethernet ports in shared spaces.
- Installing hardware keyloggers.
- Tapping cables or signals to capture raw traffic.
Why this mapping helps
Connecting attacks to OSI layers gives students and defenders a clean way to think about controls:
- Which layer is exposed?
- Which control belongs there?
- Which logs should we monitor?
Important note
Real attacks are usually multi-layered. A phishing message (often linked to layer 6 concerns) can lead to an application exploit at layer 7, and then to lateral movement through layers 3 and 2.
Educational use only: This post is for awareness and defensive learning.